Reuters reported Friday that newly declared Democratic Presidential candidate Beto O’Rourke had been part of an infamous hacker group as a teen. (Hacking is illegal unethical, don’t you know.)
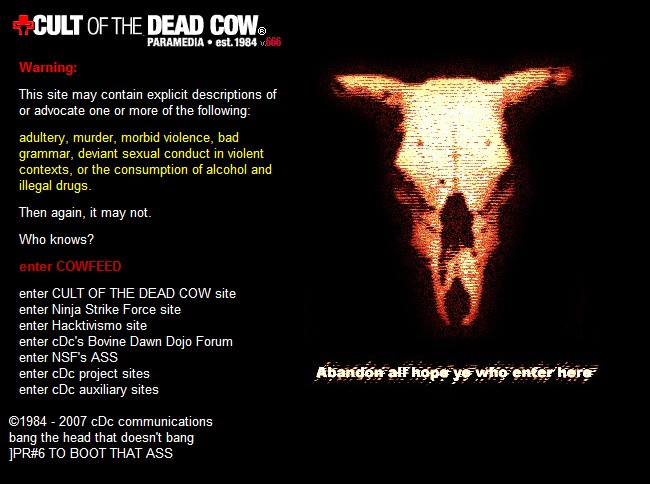
Reporter Joe Menn said that he learned about O’Rourke’s involvement in the group when he began researching The Cult of the Dead Cow, which he called “the most interesting and influential hacking group in history.”
He discovered that an alumnus of the group had a member who was sitting in Congress. “I didn’t know which one,” Menn said, “and then I figured out which one it was. And the members of the group wouldn’t talk to me about who it was. They wouldn’t confirm that it was this person unless I promised that I wouldn’t write about it until after the November 2018 election,” that being O’Roarke’s unsuccessful effort to defeat Texas Senator Ted Cruz last year. Reuters, to be clear, sat on the story, which may have interested Texas voters, for two years.
O’Rourke himself eventually agreed to talk on the record in an interview in late 2017, confirming that he was a member of the group ,also on the understanding that the information would not be made public until after his Senate race against Cruz .
The ethics takeaways from this are irrelevant to how much weight a voter should put on youthful, pre-adulthood conduct by candidates. But these aren’t ugly or stupid tweets we’re talking about, it is criminal activity–conduct. The public has a right to know, and voters particularly have a right to know. Journalists have a great deal of discretion regarding the promises they make to sources and subjects of investigations, but promising to hide information about a candidate until an election has taken place can’t be defended. It’s a breach of trust, even if it involves high school conduct. Would Menn have made that promise if the adolescent conduct involved selling drugs? Stealing cars? Setting up burning crosses on black citizen’s lawns? Beating up gays? Gang rape? Setting homeless people on fire in the park? Would he have made that promise in O’Roarke were a Republican?
You know, for some strange reason, I don’t trust the judgment and motives of reporters like Menn. The rule should be that if facts come to light that a member of the public and voters would want to know to make an informed decision about their democracy, those facts should be reported immediately, and let the chips fall where they may. Yes, of course there may be rare exceptions; there always are exceptions. Somehow, helping a Democrat get elected seems to always be one. It isn’t.
The mainstream news media, you will recall, tried to bury Bill Clinton’s activities with Monica Lewinsky and the rape allegations of Juanita Broaddrick, just as, in those halcyon days when everybody foolishly thought journalists were fair and unbiased, White House pool reporters covered up impeachable liaisons by Jack Kennedy. What other secrets have they buried to help their favorite politicians? I don’t know. That’s the scary part.
Reuters, if it cares about journalism integrity, should fire Menn, and send a loud message that a reporter withholding information about a candidate until after it is too late to influence the election just because the candidate wants him to is taboo in the field. Of course, it won’t.
Yet another reason I will never vote Democrat. They are all crooks, but I am being force fed one side…
Point of order, in the interest of fairness – “Hacking” isn’t illegal, just like “Immigration” isn’t illegal. You can illegally immigrate, or you can illegally hack something, but context matters. Same applies to describing hacking as “unethical”. [above: (Hacking is illegal unethical, don’t you know.)]
[I haven’t read anything on this story yet, what his involvement might have been within the group, or what the group has done or been accused of doing. I make no comment or defense to O’Roarke’s specific situation.]
From Technopedia: Hacking Definition – What does Hacking mean?
Hacking generally refers to unauthorized intrusion into a computer or a network. The person engaged in hacking activities is known as a hacker. This hacker may alter system or security features to accomplish a goal that differs from the original purpose of the system.
That describes a cyber-crime. It is also the kind of hacking that the Dead Cow hackers engaged in.
I don’t think “immigration” is a good analogy. A better one would be murder. There are legal forms of murder, but the statement “murder is a crime” clearly refers to the kinds of murder that are a crime, just like “hacking is a crime.”
Things I’ll note:
1) “Generally” does not mean “Always”
2) “Hacking” is an activity and can be authorized (are you saying that law enforcement investigators that defeat security protocols on a suspect’s cell phone, under warrant and court authorization, criminals?)
3) You left out this part from your source definition: Hacking can also refer to non-malicious activities, usually involving unusual or improvised alterations to equipment or processes.
(Good to know about “Dead Cow” – off topic of my post, but good to know, as I said: I don’t know anything about that group or O’Roarke and his involvement.)
1) Agreed, but a definition of a word that is generally uses is legitimately referred to as its meaning as t5he word is “generally” understood.
2) No, but the reason they have to get prior authorization is because they WOULD be criminals if they didn’t. “Breaking into a house” that isn’t your own is “generally” a crime, but a court can authorize that too.
3) I did leave it out, because a second meaning isn’t relevant if one correctly uses the first.
Admittedly, I get stuck on semantics – so when I see “Hacking is illegal, you know” – it just seems too basic, broad, and devoid of fair consideration, particularly to the White Hat Hackers out there and the kids that brute force hacked the 4-digit TV parental controls password by guessing each 4 digit password between 0000 and 9999. I think the nuance is important to maintain – as important as saying “alleged killer”. It may seem a foregone conclusion, but you aren’t doing it for yourself, you’re doing it to set a good example.
I thought that murder was, by definition, the unlawful and premeditated killing of a human being? You’re saying that it’s just premeditation that defines it from manslaughter?
…and malice aforethought?
It is; I was careless. I meant homicide.
…the idea being a word we usually associate with a crime, but with which there are exceptions. Stupid mistake. I’m going to flagellate myself now.
Tim,
I am interested in the definition you use in claiming hacking isn’t illegal. It seems counterintuitive, and I am looking to learn how you arrived at that conclusion
No snark; I am open minded on a topic I feel I am better informed than the average citizen (and thus want to learn)
I’ll use Jack’s definition from above, but I’ll include the whole thing:
https://www.techopedia.com/definition/26361/hacking
From Technopedia: Hacking Definition – What does Hacking mean?
Hacking generally refers to unauthorized intrusion into a computer or a network. The person engaged in hacking activities is known as a hacker. This hacker may alter system or security features to accomplish a goal that differs from the original purpose of the system.
Hacking can also refer to non-malicious activities, usually involving unusual or improvised alterations to equipment or processes.
Also, I’ll add this additional resource from Jack’s chosen site of authority:
https://www.techopedia.com/definition/10349/white-hat-hacker
So to answer your question, I suppose I have a “personal definition” that more aligns to accept a neutral nature to hacking “defeating processes and controls to attain a desired outcome in an unconventional way”
In my world, social engineering is a form of hacking. Two examples of this would be 1) to call someone on the phone and gain their trust to tell you who personal information so you could change their password and take control of their account or 2) place yourself at a bar you know to be a favorite place of a potential investor so you can pitch a business idea informally without going through their administrative staff or other controls or processes.
Good people are out there who seek “Bug Bounties” for software bugs. The bounties are offered by the makers of the software and they invite hackers to search for bugs and report their findings. The difference seems to be that a “Security Researcher” reports bugs and a “Hacker” sells or exploits bugs. But there’s a point in time when a person finds the bug where they are not yet a researcher or a hacker until they decide what to do with the information, though their actions are completely the same to that point.
I thought that was where your head space resided. While the group in question were in no respect ‘white hats’ and thus could credibly be called ‘criminals,’ not ALL hackers are criminals.
Having permission is the key point.
Thanks for taking the time to elaborate.
I used 2 links – oops. Awaiting moderation.
O’Rourke is misspelled in the title.
My subtle protest against St. Patrick’s Day.
Ah, the day that the world comes together to celebrate orthodox Trinitarian theology, to venerate devout missionary fervor for spreading Christianity, to convert by the thousands, and to aggressively topple the symbols of paganism…?
That is what we celebrate on St. Patrick’s Day…?
Right?
I was immersed in St. Patrick’s Day in Boston. Never made sense to me; a narrow market ethnic celebration that’s an excuse to wear green and get drunk. Even dumber than New Years, which is amazing.